Why is asymmetric key more secure
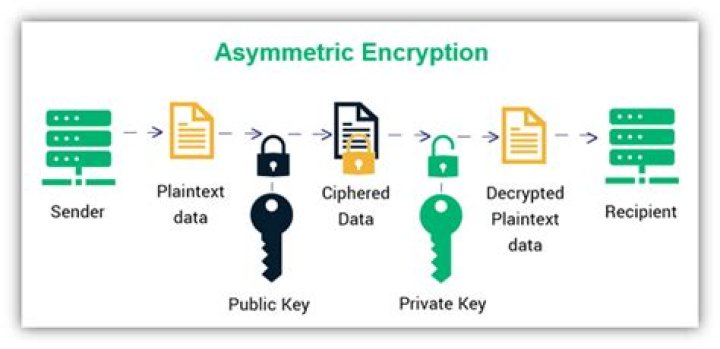
Asymmetric cryptography offers better security because it uses two different keys — a public key which only gets used to encrypt messages, making it safe for anyone to have, and a private key to decrypt messages that never needs to be shared.
Is asymmetric encryption secure?
Increased data security is the primary benefit of asymmetric cryptography. It is the most secure encryption process because users are never required to reveal or share their private keys, thus decreasing the chances of a cybercriminal discovering a user’s private key during transmission.
What is an advantage asymmetric key encryption has over symmetric key encryption?
The main advantage of symmetric encryption over asymmetric encryption is that it is fast and efficient for large amounts of data; the disadvantage is the need to keep the key secret – this can be especially challenging where encryption and decryption take place in different locations, requiring the key to be moved …
Is symmetric or asymmetric encryption faster?
Two different keys are now involved in encrypting and decrypting the data. Symmetric encryption is comparably much faster than asymmetric encryption, which is why it is still used massively today.What is the difference between asymmetric and symmetric encryption and which one is better?
Symmetric Key EncryptionAsymmetric Key EncryptionIt only requires a single key for both encryption and decryption.It requires two key one to encrypt and the other one to decrypt.
Which is the largest disadvantage of the symmetric encryption?
9. Which is the largest disadvantage of symmetric Encryption? Explanation: As there is only one key in the symmetrical encryption, this must be known by both sender and recipient and this key is sufficient to decrypt the secret message.
Why is asymmetric encryption slower?
Asymmetric encryption is slower than symmetric encryption due to the former’s longer key lengths and the complexity of the encryption algorithms used. … In order to maintain security, asymmetric encryption must make it too difficult for a hacker to crack the public key and discover the private key.
Why is symmetric encryption used?
Due to the better performance and faster speed of symmetric encryption (compared to asymmetric), symmetric cryptography is typically used for bulk encryption / encrypting large amounts of data, e.g. for database encryption.What advantages do asymmetric algorithms have over symmetric ones?
What advantages do asymmetric algorithms have over symmetric ones? they allow secure communication over insecure channels; By exchanging public keys for encrypting data, asymmetric encryption securely exchanges information over untrusted channels.
What is a difference between symmetric and asymmetric encryption algorithms?Symmetric encryption uses a single key that needs to be shared among the people who need to receive the message while asymmetric encryption uses a pair of public key and a private key to encrypt and decrypt messages when communicating.
Article first time published onHow fast is symmetric encryption?
In general case, symmetric cryptography is not faster that asymmetric ones. For example with this asymmetric cryptosystem we are able to encrypt more than 40Gb per second. This huge number is not comparable with slow systems such as 1024-bit RSA that is 40Kb.
Why do we need both symmetric and asymmetric encryption?
Symmetric keys use the same key for both encryption and decryption. … Vice versa, if users with the private key sign some data then anyone with the public key can decrypt and verify the integrity and authenticity of that data. Asymmetric is more beneficial when larger subsets of entities are sharing information.
What is asymmetric and symmetric encryption discuss the pros and cons of asymmetric encryption and symmetric encryption?
Mailfence uses Symmetric and Asymmetric encryption as each method has its pros and cons. … Symmetric encryption uses the same key to encrypt and decrypt data making it very easy to use. Asymmetric encryption uses a public key to encrypt data and a private key to decrypt information.
Is public key encryption more secure from cryptanalysis than symmetric encryption?
One is that public-key encryption is more secure from cryptanalysis than symmetric encryption. … For public-key key distribution, some form of protocol is needed, often involving a central agent, and the procedures involved are no simpler or any more efficient than those required for symmetric encryption.
Which encryption technique is more effective and why?
Advanced Encryption Standards (AES) The Advanced Encryption Standard (AES) is the algorithm trusted as the standard by the U.S. government and many other organizations. Although it is extremely efficient in 128-bit form, AES encryption also uses keys of 192 and 256 bits for heavy-duty encryption.
Is multiple encryption more secure?
Does double encryption increase security? It depends, but not always. … However, the use of multiple ciphers requires a password at each level, each of which is theoretically as vulnerable (or as secure) as the first encryption password.
What is the difference between symmetric and symmetrical?
“Symmetrical” is a non-technical term, to describe any object that has symmetry; for example, a human face. “Symmetric” means “relating to symmetry”, and is also used in a number of technical mathematical contexts (see Sam Lisi’s comment under the question).
Is AES asymmetric or symmetric?
Is AES encryption symmetric or asymmetric? AES is a symmetric encryption algorithm because it uses one key to encrypt and decrypt information, whereas its counterpart, asymmetric encryption, uses a public key and a private key.
Is asymmetric encryption slower than symmetric encryption?
Asymmetric encryption is far slower than symmetric encryption, and is also weaker per bit of key length. The strength of asymmetric encryption is the ability to securely communicate without pre-sharing a key. Table 4.16 compares symmetric and asymmetric algorithms based on key length.
What are the limitations of asymmetric encryption?
- It is a slow process. …
- Its public keys are not authenticated. …
- It risks loss of private key, which may be irreparable. …
- It risks widespread security compromise.
What is the main problem with the asymmetric encryption?
The problem is that this scheme cannot discriminate between the two individuals who know the shared key. For example, your pen pal may fraudulently send messages using your shared key, pretending to be you.
Which of the following is asymmetric encryption algorithm?
RSA is an algorithm used by modern computers to encrypt and decrypt messages. It is an asymmetric cryptographic algorithm. Asymmetric means that there are two different keys. This is also called public key cryptography, because one of them can be given to everyone.
Which of the following algorithm uses asymmetric encryption?
RSA Asymmetric Encryption Algorithm Invented by Ron Rivest, Adi Shamir, and Leonard Adleman (hence “RSA”) in 1977, RSA is, to date, the most widely used asymmetric encryption algorithm.
Is it better to always encrypt data?
This is one of the reasons why we recommend you use Always Encrypted to protect truly sensitive data in selected database columns. One thing to call out is the fact that by encrypting data on the client-side, Always Encrypted also protects the data, stored in encrypted columns, at rest and in transit.
What is one of the advantages of using both symmetric and asymmetric cryptography in SSL TLS?
SSL/TLS uses both asymmetric and symmetric encryption to protect the confidentiality and integrity of data-in-transit. Asymmetric encryption is used to establish a secure session between a client and a server, and symmetric encryption is used to exchange data within the secured session.
What are the two components of an asymmetric encryption system?
Asymmetric Encryption uses two distinct, yet related keys. One key, the Public Key, is used for encryption and the other, the Private Key, is for decryption. As implied in the name, the Private Key is intended to be private so that only the authenticated recipient can decrypt the message.
What are the two requirements for secure use of symmetric encryption?
What are the two principal requirements for the secure use of symmetric encryption? (1) a strong encryption algorithm; (2) Sender and receiver must have obtained copies of the secret key in a secure fashion and must keep the key secure.
What is meant by asymmetric encryption?
Asymmetric encryption (also known as asymmetric cryptography) allows users to encrypt information using shared keys. You need to send a message across the internet, but you don’t want anyone but the intended recipient to see what you’ve written.
What is the difference between symmetric and asymmetric in chemistry?
A symmetrical molecule is one whose appearance does not change if you turn it about an axis of symmetry; original and rotated states are indistinguishable from one another. By contrast, an asymmetrical molecule has no axis of symmetry; you can tell if it has been rotated.
What is the difference between the symmetric and asymmetric models of communication?
The difference between the symmetric and asymmetric models of communication is that symmetrical communication provides a more balanced form of communication between the organization and its publics instead of one party having more power than the other in asymmetrical communication.
What are the disadvantages of symmetric key cryptography?
Symmetric cryptosystems have a problem of key transportation. The secret key is to be transmitted to the receiving system before the actual message is to be transmitted. Every means of electronic communication is insecure as it is impossible to guarantee that no one will be able to tap communication channels.