How do I secure my AWS server
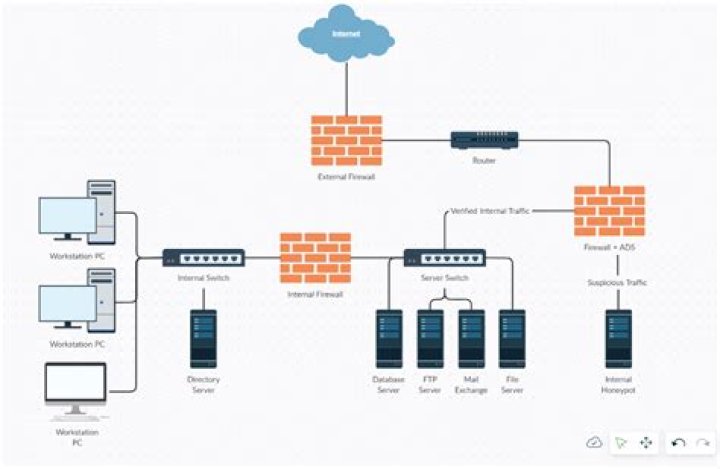
Use the Advisor Tool. … Categorize AWS assets. … Design your company’s Information Security Management System (ISMS). … Manage AWS Accounts, Groups, and Roles. … Design your AWS strategy to maximize security. … Manage AWS credentials. … Use IAM roles for delegation and temporary security credentials.
How do I secure my AWS root account?
- Use IAM users for day-to-day access to your account, even if you’re the only person accessing it.
- Eliminate the use of root access keys. Instead, rotate them to IAM access keys, and then delete the root access keys.
- Use an MFA device for the root user of your account.
How do I secure my cloud instance?
- Encryption of data in transition must be end to end. …
- Encryption is important for data at rest, too. …
- Vulnerability testing should be rigorous and ongoing. …
- Have a defined and enforced data deletion policy. …
- Add protective layers with user-level data security. …
- Get a virtual private cloud and network.
How do I secure my cloud services?
- Use a Cloud Service That Encrypts. …
- Read the User Agreements. …
- Set Up Your Privacy Settings. …
- Use Strong Passwords. …
- Use Two-Factor Authentication. …
- Don’t Share Personal Information. …
- Don’t Store Sensitive Information. …
- Use a Strong Anti-Malware Program.
What is more secure IAM user or IAM role?
Roles are essentially the same as Users, but without the access keys or management console access. … This enables the user to request short-term credentials from AWS STS, which is more secure than attaching the permissions directly to the user’s access keys.
Is it safe to share AWS account ID?
Sharing AWS Account numbers is fairly safe among business partners. There is not much if anything that anyone can do with just the account number. To assume a role, the account number is required, but the authorizing account must also setup a trust relationship for the policy.
Which of the following steps does the most to protect your AWS account?
MFA is the best way to protect accounts from inappropriate access. Always set up MFA on your Root user and AWS Identity and Access Management (IAM) users. If you use AWS Single Sign-On (SSO) to control access to AWS or to federate your corporate identity store, you can enforce MFA there.
Which is the most secure cloud storage?
- IDrive. IDrive furnish a constant sort of your records, even those on network drives. …
- pCloud. pCloud is one of the relatively few secure cloud services that offer lifetime participation; you essentially get a virtual, perpetual cloud drive. …
- Sync.com. …
- Microsoft OneDrive. …
- Google Drive. …
- Egnyte Connect. …
- MEGA. …
- Tresorit.
Can clouds be hacked?
Files stored on cloud servers are encrypted. That means the data is scrambled, making it much more difficult for hackers to access.
How do you secure a service?- Establish and Use a Secure Connection.
- Use SSH Keys Authentication.
- Secure File Transfer Protocol.
- Secure Sockets Layer Certificates.
- Use Private Networks and VPNs. Server User Management.
- Monitor Login Attempts.
- Manage Users. Server Password Security.
- Establish Password Requirements.
What tools can be used to secure cloud data?
- Bitglass. Bitglass, currently in beta, provides transparent protection for your business’s data. …
- Skyhigh Networks. Skyhigh Networks discovers, analyzes and secures your use of cloud applications. …
- Netskope. …
- CipherCloud. …
- Okta.
What kind of security does AWS use?
CategoryUse casesAWS serviceDetectionSecurity management for IoT devicesAWS IoT Device DefenderInfrastructure protectionNetwork securityAWS Network FirewallDDoS protectionAWS ShieldFilter malicious web trafficAWS Web Application Firewall (WAF)
When should you use AWS IAM roles VS users?
An IAM user has permanent long-term credentials and is used to directly interact with AWS services. An IAM role does not have any credentials and cannot make direct requests to AWS services. IAM roles are meant to be assumed by authorized entities, such as IAM users, applications, or an AWS service such as EC2.
How do I share my AWS account?
- Sign in to the AWS Management Console as the root user.
- Open the AWS Support Center.
- Choose Create case.
- Enter the details of your case: Choose Account and billing support. …
- For Preferred contact language, choose your preferred language.
How do I find my IAM role in AWS?
- Click Amazon DynamoDB in the Select service dropdown list.
- Click Select All to simulate all DynamoDB actions for your role.
- Click RDS in the Select service dropdown list.
- Click Select All to test all RDS actions for your role.
Should I keep my AWS account ID secret?
While divulging the ID does not directly expose an account to compromise, an attacker can leverage this information in other attacks. A reasonable effort should be made to keep AWS account IDs private, but in practice, they are often exposed to the public unintentionally.
Is AWS account ID a secret?
Every AWS account is uniquely identified by this 12 digit number, and while this ID is usually kept private, they can all too easily be exposed to the public.
Is AWS Arn private?
Well, from a security point of view, it’s never bad to give people less information. But, as long as you have sensible security policies in AWS, there is no reason that an arn has to be considered secret.
How do I make sure I can access my data?
Tap the “Mobile data” slider. This will toggle your mobile data ON. On older versions of Android, check the “Data enabled” box. Note: Your plan will need to support mobile data in order for you to enable it. You will also need a cellular signal in order to use your mobile data connection.
Is Google Drive secure?
Google Drive is generally very secure, as Google encrypts your files while they’re being transferred and stored. However, Google can undo the encryption with encryption keys, meaning that your files can theoretically be accessed by hackers or government offices.
Can local storage be hacked?
Local storage is bound to the domain, so in regular case the user cannot change it on any other domain or on localhost. It is also bound per user/browser, i.e. no third party has access to ones local storage. Nevertheless local storage is in the end a file on the user’s file system and may be hacked.
How secure are AWS servers?
AWS security is not fail-safe and operates on a Shared Security Responsibility model. This means that Amazon secures its infrastructure while you have your own security controls in place for the data and applications you deploy and store in the cloud.
Is AWS secure?
With AWS you can build on the most secure global infrastructure, knowing you always own your data, including the ability to encrypt it, move it, and manage retention. … Additional encryption layers exist as well; for example, all VPC cross-region peering traffic, and customer or service-to-service TLS connections.
Is Google Drive more secure than OneDrive?
When it comes to account security and privacy, Google Drive and OneDrive are comparable. The main difference is that Google mines user data from files uploaded to Google Drive (for non-malicious reasons, but it does so nonetheless).
How do I secure my cloud infrastructure?
- Make sure the cloud system uses strong data security features. …
- Backups must be available as well. …
- Test your cloud system on occasion. …
- Look for redundant storage solutions. …
- Allow your system to use as many data access accounts and permissions as possible.
What are your first three steps when securing a server?
- Step 1 – Shut Down Access.
- Step 2 – Patch Your Servers.
- Step 3 – Tightly Control User Access.
How do I setup a secure home server?
- Only Open Ports You Need To. …
- Use CloudFlare for DNS and DDOS protection. …
- Don’t Expose These Services. …
- Use a Reverse Proxy Manager. …
- Keep Your System Updated. …
- Trust Your Sources. …
- BACKUP Your Server. …
- Don’t give access to anything that doesn’t need access.
What are cloud security controls?
Cloud security control is a set of security controls that protects cloud environments against vulnerabilities and reduces the effects of malicious attacks. A wide-ranging term, cloud security control includes all of the best practices, procedures, and guidelines that have to be implemented to secure cloud environments.
What is cloud security in cyber security?
Cloud security is a discipline of cyber security dedicated to securing cloud computing systems. This includes keeping data private and safe across online-based infrastructure, applications, and platforms. … Cloud providers host services on their servers through always-on internet connections.
What does a Cspm do?
Cloud security posture management (CSPM) automates the identification and remediation of risks across cloud infrastructures, including Infrastructure as a Service (IaaS), Software as a Service (Saas), and Platform as a Service (PaaS).
How do I assume AWS role?
You can assume a role by calling an AWS CLI or API operation or by using a custom URL. The method that you use determines who can assume the role and how long the role session can last. ¹ Using the credentials for one role to assume a different role is called role chaining.